Mimblewimble Protocol - Crypto Academy / S4W2 - Homework Post for @fredquantum / By @bukkyi4u
1 comment
edited with canva
INTRODUCTION
First and foremost, congratulations, Sir, @fredquantum for your new appointment as a Steemit Crypto Academy professor in this new season. It gives me great pleasure to be participating in your lecture for the first time. Have a nice read.

BACKGROUND
The introduction of the blockchain technology and its incorporation into a lot of our traditional way of doing things along with its disruptive capacity came with quite a number of good benefits. Some of these benefits include top-notch security, immutability, traceability, transparency and a few other variables.
One very critical aspect of the blockchain technology that has drawn widespread attention and discussion is the concept of privacy. How this novel technology handles it is important. It is worthy of note that the blockchain conceals the names behind every transaction while transparently making such transactions available and verifiable to the public.
One important blockchain of interest is the Bitcoin network. The Bitcoin network displays information relating to a particular transaction on its public blockchain. So, it displays such information as the address, timestamp, the amount of asset transacted among a few other pieces of information. This is exactly the point as this information still reveals some details whose privacy would have been appreciated. The Mimblewimble protocol seems to have some desirable features in this regard.

WHAT IS THE MIMBLEWIMBLE BLOCKCHAIN PROTOCOL?

copyright free image from pixabay
The Mimblewimble blockchain protocol simply refers to a blockchain solution which makes it possible for transactions to be carried out on the platform in a highly secured manner without having to reveal the amounts transacted as well as the addresses behind every transaction. Equally, it boasts of a distributed ledger system that is a lot more compact and which removes redundant transaction data from the network.
This blockchain protocol which could be a great solution to the privacy and scalability issue of the Bitcoin network has drawn mixed reactions as to how it could be implemented to that effect. However, the popular speculated solution is its use as a side chain for the network. Some cryptos like Beam and Grin have implemented these and a Mimblewimble testnet has been launched in 2020 for Litecoin as a way of making its scaling and privacy better.
Tom Elvis Jedusor became known for introducing the design for the Mimblewimble protocol in the middle of 2016. This figure was pseudonymous and the core concepts he described in the original document of the Mimblewimble protocol were received with some doubts and questions to be cleared.
Andrew Poelstra took it upon himself as a blockstream researcher to undertake an extensive study and research into the concept in order to come up with some noteworthy improvements to the original ideas published in the first document. Consequently, he made a publication in October 2016 with the title Mimblewimble to that effect.
The Cryptography Of The Mimblewimble Blockchain Protocol
In describing how the Mimblewimble protocol really works without having to X-ray in-depth specifics and proofs I would mention the three cryptographic methodologies it employs viz a viz:
- Elliptic Curves:- This principle of the protocol is used for public key cryptography. It is helpful in ensuring that transactions can be transmitted between different points or addresses without the public knowing the source of the transaction.
- Commitments:- This works like a public box which can be locked. It operates with the principle of hiding and binding. In this way a transaction can be hidden and binded, then transmitted to the receiver. Since it is binded its details cannot be viewed by the public. The receiver is able to unlock it with a private key.
- The Mimblewimble:- This uses the zero-sum concept to ensure that amount transferred as input is the same as that received as output. This maintains the originality and verifiability of the transaction. The second is the possession of private Elliptic Curve Cryptographic keys which gives the receiver exclusive access to the details of the transaction.
However, you can access an original in-depth description here.

Discuss in detail how the Mimblewimble blockchain protocol works.

copyright free image from pixabay
Actually, the Mimblewimble blockchain protocol works by changing how blockchain transactions had originally been modelled like. What it does is that it makes it possible for a faster and easier compact history of the blockchain to be downloadable, synchronisable and verifiable.
Usually, the blockchain works by obscuring the addresses. This means that an outsider would only see a transaction as random data. However, the details of the transaction are actually visible to the participants who had engaged in it. So, rather than a transaction coming out as many different data the Mimblewimble protocol simply presents it as a single transaction.
Consequently, the verification of blocks is undertaken without revealing details of every transaction. Be that as it may, individual inputs can never be back-traced to their respective outputs.
By way of illustration let us consider the scenario below:
- Eunice receives 7 Beam coins from her mother
- Equally, she receives 3 Beam coins from her father
- She, in turn, transfers the 10 Beam coins to Gabriel
- All of these transactions have been verified without their details being made available publicly
- Gabriel only understands that Eunice had sent him 10 Beam coins
- He is unable to decipher from whom Eunice had received the coins previously
As a requirement for moving coins on the Mimblewimble blockchain protocol some important information for verification must have been exchanged between the receiver and sender. This means that Eunice and Gabriel would have to communicate. However, the two participants being online at the same time is not a necessity.
Another interesting feature of the Mimblewimble blockchain protocol is its use of the cut-through feature. This enables it to reduce the volume of block data by removing information relating to transactions which are considered redundant. So, in the illustration I gave above, rather than the blockchain recording every single input and output - that is, taking into cognizance the inputs, first from each of Eunice's parents to her and then from Eunice herself to Gabriel - the chain would simply record the one single input and output which pairs from Eunice herself to Gabriel.

Discuss in detail your understanding of Confidential Transactions (CTs).

copyright free image from pixabay
Also, known as Confidentials Transactions (CT), Confidential Transactions (CTs) simply refers to a type of Zero Knowledge Protocol (ZKP) which has been employed by some blockchain protocols that make use of cryptography as a way of making the transactions that occur on the blockchain to remain anonymous and private to the participants.
These transactions can be validated and verified on the network even when they are encrypted. Consequently, it is not possible to see the exact amount linked to every single transaction. Interestingly, even the issuers as well as the recipients have these concealed from them.
How It Works:-
As has been seen with the Bitcoin network, it is possible for the nodes to know the amount to be transferred to the receiving address and from where. With the implementation of Confidential Transactions things work in a more complex way. Here an advanced form of cryptography is employed such that data relating to a transaction has to be hidden together with the data from other transactions.
Nonetheless, such a transaction is verifiable even without being revealed. In the Monero network, a certain Pedersen Commitment, which allows a transaction to be completed without having to reveal the address is used. This makes use of blind signatures in place of addresses.
Generally, the outsiders to the transaction can only see encrypted information. This would help in verifying that a transaction was actually made. The cryptographic function employs the use of a hash for the purpose of concealing the data. However, this hash can be signed digitally and this acts as a proof that the transaction did occur without revealing its details.

How do you think Mimblewimble Protocol can be utilized on the Bitcoin Network to enable anonymity of transactions and improve scalability?

copyright free image from pixabay
The Bitcoin network has suffered from issues of fungibility and privacy as a serious setback. In proffering a solution, Adam Back, the Blockstream CEO, in 2013 postulated that a protocol which would work by encrypting the details involved in every single transaction, thereby allowing only the participants to have knowledge of them, was quite necessary. This idea was supported by Gregory Maxwell, an important figure in blockchain technology.
Subsequent research following the work and publication of Andrew Poelstra (earlier mentioned) on Mimblewimble has been carried out by several developers in trying to understand how the MW protocol can be successfully implemented or explored. They have noted that although it wouldn't be technically impossible, using it with the Bitcoin network may come with some difficulty. Nonetheless, the postulations made by the researchers and Poelstra himself suggests that this protocol could function better as a sidechain solution in improving the Bitcoin network.
So, in line with that finding, employing Mimblewimble protocol as a sidechain to the parent Bitcoin network can work in two ways by:
- Leveraging the Confidential Transactions (CTs) of the proposed protocol
- Leveraging the Cut-through compact-style data management strategy to eliminate redundant transactions data
The Mimblewimble protocol can be employed as a sidechain - just like the Lightning Network - to the Bitcoin network in order to leverage the two important technologies of the protocol which I mentioned above as a solution to the Bitcoin network problem of privacy and scalability.
Implementing Confidential Transactions (CTs):-
Introducing the Mimblewimble protocol to the Bitcoin network would ensure that unlike the Bitcoin which keeps record of every single transaction which has been made even from The Genesis block for verification purposes, only the most essential data would be recorded with the Mimblewimble protocol while equally maintaining privacy.
Interestingly, the Mimblewimble protocol would also eliminate the scripting system of Bitcoin; this would ensure more privacy by concealing addresses.
Implementing Cut-through Feature
One other key interesting feature is the cut-through feature. This particular feature would help increase scalability by making use of a compact-style data management. This means that redundant transaction data is not recorded. Hence, only the most important data is represented on the chain. This even makes for less computational energy usage.

State the Pros and Cons of the Mimblewimble protocol.

copyright free image from pixabay
PROS OF THE MIMBLEWIMBLE BLOCKCHAIN PROTOCOL
The MW protocol does come with some interesting advantages. Some of these advantages include:
- The MW protocol makes it possible for data to be compressed and this provides the desirable effect that the blockchain sizes become reduced generally
- Equally, it is possible for transactions to be verified by the nodes and their history loaded in a faster way while consuming much less amount of resources
- Again, it should be noted that the lightweight feature of it makes downloading and synchronising with this blockchain a lot less difficult for newer nodes.
- Generally, its mode of operation which involves a much reduced cost can make it possible for more distributed and even diversified communities to join
- The reduced cost can equally be a strong point against centralising its mining operations which has bedeviled many blockchains that are based on the PoW consensus.
- The protocol comes with a high level of scalability which would make it a good option to be used as a side chain with any other parent chain
- Also, its design could also work well in making other payment channels like the Lightning Network function a lot better
- This protocol works well in concealing the details attached to transactions and this gives it a high level of privacy
- Equally, it comes with the advantage of fungibility as the units of its coins are interchangeable seminar coins
CONS OF THE MIMBLEWIMBLE BLOCKCHAIN PROTOCOL
In spite of its inherent numerous advantages or pros, there are still a few downsides to it. Some of these include:
- The use of confidential transactions actually reduces the amount of transactions that can be obtained per second due to the fact that the data size is much larger
- Its use of digital signatures makes it difficult for it to withstand quantum computers and this opens it up to the possibility of negative attacks from them

Discuss in detail at least a Crypto that uses the Mimblewimble protocol
THE GRIN CRYPTOCURRENCY
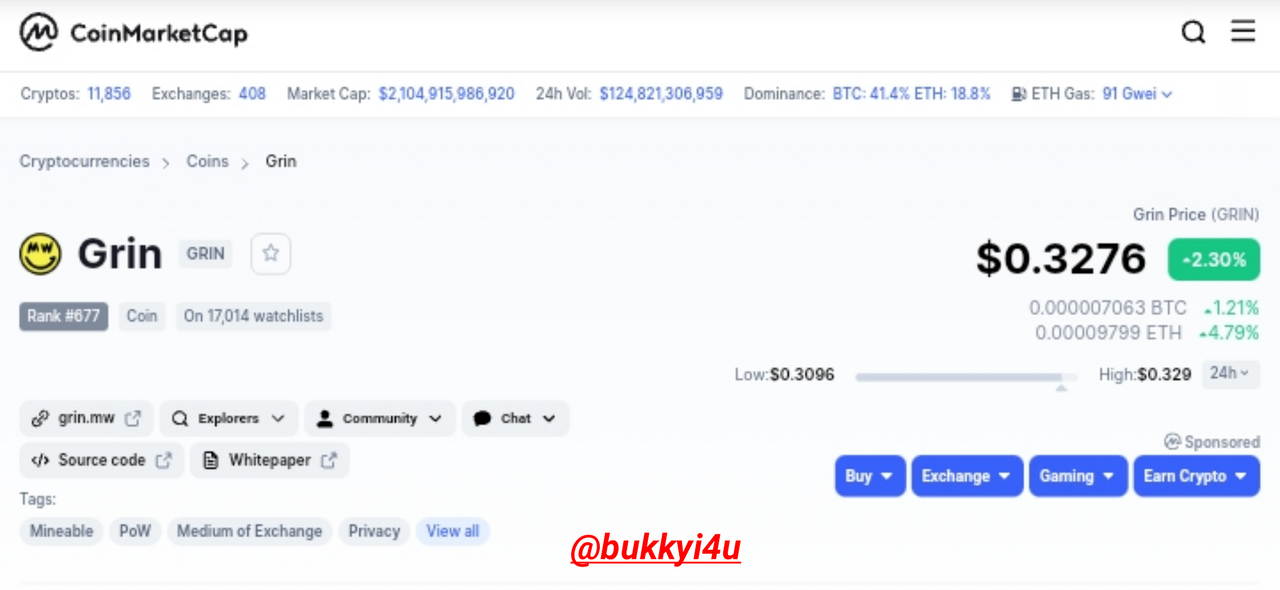
source coinmarketcap
| Parameter | Grin Crypto Statistics |
|---|---|
| Grin Price | $0.3145 |
| Price Change (24h) | $0.0009458 |
| 24h Low / 24h High | $0.3116 / $0.3235 |
| Trading Volume (24h) | $2,168,659.96 |
| Volume / Market Cap | 0.0825 |
| Market Dominance | 0.00% |
| Market Rank | #691 |
| Grin Market Cap | $26,287,285.24 |
| Fully Diluted Market Cap | $26,287,285.24 |
| All Time High | Jan 28, 2019 (3 years ago) - $10.00 (96.85%) |
| All Time Low | Nov 08, 2020 (10 months ago) - $0.2206 (42.53%) |
| Grin ROI | 96.84% |
| Grin Circulating Supply | 83,589,900 GRIN |
| Total Supply | 83,589,900 GRIN |
| Max Supply | No Data |
source:coinmarketcap
Founders And Developers:-
After Andrew Poelstra made the publication that added a few better ideas and published a technical description that was more in depth and detailed than the original white paper of the Mimblewimble that was published by Tom Elvis Jedusor, a certain Ignotus Peverell pseudonymously started working on how to ensure the implementation of this protocol.
Not quite long after, other researchers joined him in an effort which eventually metamorphosed into what is now called the Grin crypto.
Launch Date:-
After the pseudonymous Ignotus Peverell had concluded his work together with some other people who had joined him in a team to develop the Grin project, it was eventually launched on the 15th of January 2019.
Objective Of The Coin:-
Grin is a cryptocurrency that makes use of the Mimblewimble protocol. This gives it the unique feature of maintaining a balance between scalability and high level of privacy. Usually, in the chain there is no record of the amount, address and data on outputs spent in transactions. The crypto is lightweight and minimalistic.
The core of its objectives include:
- Ensuring privacy while equally enabling fungibility
- To ensure more scaling with users rather than transactions in order to preserve large space
- To ensure high-level cryptography by relying on the proven Elliptic Curve Cryptography of the Mimblewimble protocol
- Using a simple design which ensures proper auditing and simplicity
- Ensuring decentralisation of mining through the community that drives it
Operation:-
screenshot from source
The Grin cryptocurrency is driven by the community and it operates in an open-source network. Development carried out on the cryptocurrency usually comes by the voluntary involvements of contributors as well as donations since there is no individual behind it. Everybody has the opportunity of lending a voice to its development.
The crypto has a blocktime of just one minute. The coinbase reward in this one minute is actually 60 grins which means that a single grin is created per second. This is designed to remain so forever. This is a linear emission strategy which works in a disinflationary manner by steadily reducing possible rates of inflation while increasing the supply. In this manner the strategy will ensure that all participants are fairly rewarded in the distribution of the coins while equally ensuring the top-notch security of the blockchain in the long-term.
Native Blockchain:-
Grin does not make use of any public ledger. Instead, it was developed as a crypto which implements the principles of the Mimblewimble blockchain protocol. It can be accessed from its website https://grin.mw.
Availability:-
The Grin crypto can be purchased from exchanges where they are traded. Some of these exchanges include HitBTC, BKEX, KuCoin, ZT, Gate.io and some others.
HOW THE GRIN CRYPTO IMPLEMENTS THE MIMBLEWIMBLE PROTOCOL
Actually, with the Grin cryptocurrency there is no public ledger. Usually, there is no use of addresses in transactions and all the amounts sent or transfered are normally encrypted. It uses the idea of CoinJoin to implement a high level of scalability and privacy in its operations.
With the use of the Mimblewimble protocol a cryptographic method is used which ensures that data relating to past transactions can be removed without having to breach security. Thanks to this methodology, the Grin crypto does not have to worry about large amounts of uncontrollable data being left on the chain.
In ensuring that a newly created transaction has its origin properly concealed the chain ensures the relay of such a transaction among a subset of peers before it is broadcast generally.
Actually, there are a lot of other intricate features it implements due to its use of the Mimblewimble protocol and this can be obtained from the whitepaper.

CONCLUSION

While the blockchain technology comes with important benefits as traceability, security, immutability and verifiability it is saddening that such other desirable features like high-level scalability and privacy has been a problem with some including the Bitcoin network. As a great solution to this menace the Mimblewimble blockchain protocol has been unraveled.
The Mimblewimble blockchain protocol is quite interesting in its approach as it makes it possible for transactions to be verified without the details of such transactions being revealed. Hence, it conceals the addresses and the amount behind transactions. Equally, it cuts down on the size of transaction data. These combined give it privacy and high scalability as advantages.
The Mimblewimble protocol has been proposed as a side chain solution for the Bitcoin network. This would ensure that the Bitcoin network benefits from the Confidential Transactions and Cut-through features of the protocol to improve privacy and scaling.
Interestingly, some cryptos like the Grin crypto have started implementing the Mimblewimble blockchain protocol. Actually, I do hope to see a lot of other blockchain solutions that would want to take after the concept idealized by the Mimblewimble protocol.

Comments